【预警类型】高危预警
【预警内容】
CVE-2021-1675 Windows Print Spooler RCE EXP
安全公告编号:CVE-2021-1675
一、漏洞概述
6月9日,微软发布6月安全更新补丁,修复了50个安全漏洞,其中包括一个Windows Print Spooler权限提升漏洞(CVE-2021-1675)。
Print Spooler是Windows系统中用于管理打印相关事务的服务,虽然微软在公告中将该漏洞标记为Important级别的本地权限提升漏洞,但实际上在域环境中合适的条件下,无需任何用户交互,未经身份验证的远程攻击者就可以利用该漏洞以SYSTEM权限在域控制器上执行任意代码,从而获得整个域的控制权。
我们认为该漏洞实际威胁等级较高,建议相关用户尽快采取措施进行防护,尤其是域控制器等服务器。
参考链接:https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-1675
二、影响范围
受影响版本
·Windows Server 2012 R2 (Server Core installation)
·Windows Server 2012 R2
·Windows Server 2012 (Server Core installation)
·Windows Server 2012
·Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
·Windows Server 2008 R2 for x64-based Systems Service Pack 1
·Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
·Windows Server 2008 for x64-based Systems Service Pack 2
·Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
·Windows Server 2008 for 32-bit Systems Service Pack 2
·Windows RT 8.1
·Windows 8.1 for x64-based systems
·Windows 8.1 for 32-bit systems
·Windows 7 for x64-based Systems Service Pack 1
·Windows 7 for 32-bit Systems Service Pack 1
·Windows Server 2016 (Server Core installation)
·Windows Server 2016
·Windows 10 Version 1607 for x64-based Systems
·Windows 10 Version 1607 for 32-bit Systems
·Windows 10 for x64-based Systems
·Windows 10 for 32-bit Systems
·Windows Server, version 20H2 (Server Core Installation)
·Windows 10 Version 20H2 for ARM64-based Systems
·Windows 10 Version 20H2 for 32-bit Systems
·Windows 10 Version 20H2 for x64-based Systems
·Windows Server, version 2004 (Server Core installation)
·Windows 10 Version 2004 for x64-based Systems
·Windows 10 Version 2004 for ARM64-based Systems
·Windows 10 Version 2004 for 32-bit Systems
·Windows 10 Version 21H1 for 32-bit Systems
·Windows 10 Version 21H1 for ARM64-based Systems
·Windows 10 Version 21H1 for x64-based Systems
·Windows 10 Version 1909 for ARM64-based Systems
·Windows 10 Version 1909 for x64-based Systems
·Windows 10 Version 1909 for 32-bit Systems
·Windows Server 2019 (Server Core installation)
·Windows Server 2019
·Windows 10 Version 1809 for ARM64-based Systems
·Windows 10 Version 1809 for x64-based Systems
·Windows 10 Version 1809 for 32-bit Systems
三、漏洞防护
3.1官方升级
目前微软官方已针对支持的系统版本发布了修复该漏洞的安全补丁,强烈建议受影响用户尽快安装补丁进行防护,官方下载链接:
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-1675
注:由于网络问题、计算机环境问题等原因,Windows Update的补丁更新可能出现失败。用户在安装补丁后,应及时检查补丁是否成功更新。
右键点击Windows图标,选择“设置(N)”,选择“更新和安全”-“Windows更新”,查看该页面上的提示信息,也可点击“查看更新历史记录”查看历史更新情况。
针对未成功安装的更新,可点击更新名称跳转到微软官方下载页面,建议用户点击该页面上的链接,转到“Microsoft更新目录”网站下载独立程序包并安装。
3.2临时防护措施
若相关用户暂时无法进行补丁更新,可通过禁用Print Spooler服务来进行缓解:
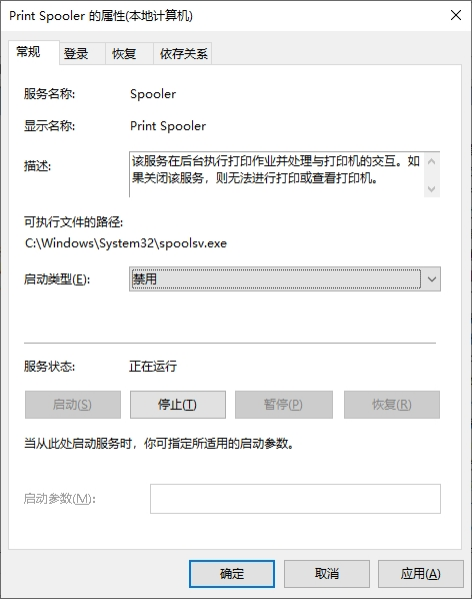
一:在服务应用(services.msc)中找到Print Spooler服务。
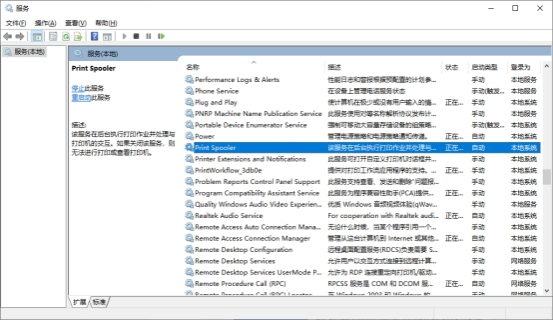
二:停止运行服务,同时将“启动类型”修改为“禁用”。